Effective Ways to Protect SIP Connections
|
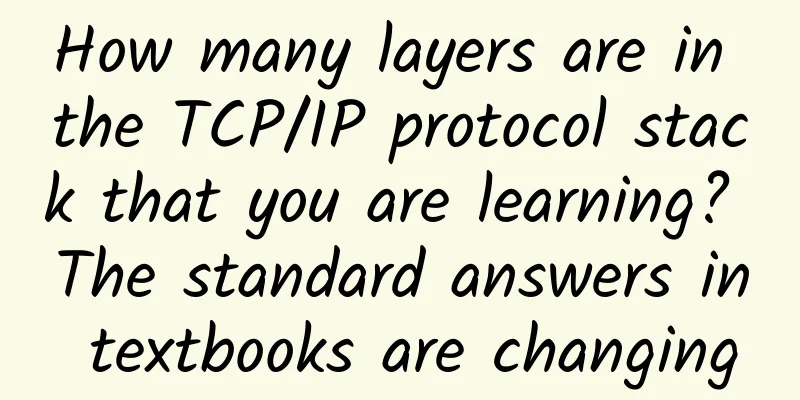
Session Initiation Protocol (SIP) is the underlying standard that governs how devices communicate over the Internet. Like most security issues, a defense-in-depth strategy is necessary to protect SIP. That way, even if one security layer fails, another layer is there to provide protection. Next, let's look at a few technologies that can make SIP connections more secure: 1. TLS 1.3. Transport Layer Security (TLS) is a cryptographic protocol used to protect data exchanged over computer networks, and more specifically, TLS is used to protect web user data from cyberattacks. TLS 1.3 is the latest version of this cryptographic protocol and strengthens the algorithm used to encrypt Internet traffic. Check your SIP infrastructure to determine the version your network uses. To provide backward compatibility, many products use TLS 1.2 by default. Where possible, upgrade to TLS 1.3 (it should be a free upgrade) for enhanced session-level security. 2. Firewall. Don’t forget this first line of defense. Contact your security administrator to review your firewall port configuration to ensure you have the protection you need. If you have a next-generation firewall, determine if you can enable Denial of Service (DoS) protection for the SIP ports. 3. Integrated SIP firewall. Some SIP gateways (usually higher-end systems) have SIP security built in. These gateways won't replace a firewall, of course, but they may have supplemental features that can support an existing firewall. Likewise, remember to look for DoS capabilities, as this type of protection is unlikely to be available with a traditional firewall. 4. Theft of Service (ToS) Analysis . It is critical to protect SIP by protecting your SIP environment from theft of service (ToS). If an unauthorized threat actor compromises your system to make their own voice calls over IP Calling, this additional burden can result in poor voice quality and performance that can impact legitimate users. Perform regular security analysis—at least quarterly—to review call and usage logs from your SIP gateways. Calls from all over the world that have no business connection with your company could be linked to a security breach. Finally, do not use default administrator credentials on the gateway. These could be used by unauthorized individuals to compromise the security of the SIP gateway. |
<<: 5G VS Wi-Fi6: What are the differences in technology? Which one is more mature in application?
>>: 5G messaging is entering a development phase
Recommend
The final of the 2024 3rd Ruijie National College Student Information Technology Competition will be held in Fuzhou on December 28
The final and award ceremony of the 2024 3rd Ruij...
Gartner: Global 5G infrastructure market size will double to $8.1 billion in 2020
According to Gartner's latest forecast, the g...
edgeNAT newly launched Korean CN2 line native IP host monthly payment starts from 80 yuan
This month, edgeNAT launched a new Korean native ...
5G development has entered a critical period, and the following major applications are worth paying attention to in 2021
Since its official commercial launch in 2019, aft...
5G and Next Generation Networks during the COVID-19 Crisis
The word "crisis" in Chinese means both...
Average tariffs to drop by another 10%. Senior management has given operators another task target! Are you ready?
At this year's two sessions, the top leadersh...
Alibaba established the first ecological IoT alliance to open up technical standards
At the IoT Partner Program Conference 2017 (ICA) ...
HostYun: Los Angeles Cera high-security VPS starting at 19.8 yuan per month, 10G bandwidth, optional native IP
We have shared product information of many data c...
Energy-saving building 5G solutions are the key to green buildings
Building equipment suppliers are prioritizing gre...
5G user development starts with focusing on high quality
[[385400]] Recently, the Ministry of Industry and...
The Ministry of Industry and Information Technology unexpectedly disclosed the domestic 5G scheduled frequency band: starting from 3300MHz
Huawei's Kirin 970 chip pioneered the 1.2Gbps...
The Advancement of WiFi 6 Wireless Router Market Report for the First Half of 2020
In the first half of 2020, affected by the epidem...
Monitor infrastructure to prevent unexpected downtime
[[258649]] 【51CTO.com Quick Translation】Infrastru...
Edge user performance improvement solution based on multi-point coordination CoMP
1. Project Background The 5G communication networ...
Europe lags behind in 5G rollout, study shows
According to an assessment report released by the...

![[11.11] CMIVPS recharge 10% off, 30% off for all VPS annual payments, buy 10 months of dedicated server and get 2 months free](/upload/images/67cabd1b7c50a.webp)