Network equipment and protocols: protocols
|
When visiting a website and sending or receiving emails, we usually directly enter the address of the website or email address and other addresses provided by the application layer, rather than using an IP address composed of decimal numbers. However, the network layer needs IP addresses, which requires a function to map the addresses used in the application to IP addresses. In addition, IP addresses are not needed at the data link layer, but MAC addresses are needed to transmit data packets. Therefore, in actual communication, many related technologies that support IP are needed to achieve communication. IP auxiliary technologies include DNS, ARP, ICMP, ICMPv6, DHCP, NAT, etc. It also includes technologies such as IP tunnel, IP multicast, IP anycast, quality control, explicit notification of network congestion, and Mobile IP technology. 1. DNS The Domain Name System (DNS) is a service of the Internet. As a distributed database that maps domain names and IP addresses, it enables people to access the Internet more conveniently. DNS uses TCP and UDP port 53. Currently, the length of each domain name is limited to 63 characters, and the total length of the domain name cannot exceed 253 characters. (1) DNS query process Take querying zh.wikipedia.org as an example: the client sends a query message "query zh.wikipedia.org" to the DNS server. The DNS server first checks its own cache and returns the result directly if the record exists. If the record is aged or does not exist, then:
(2) View and modify DNS As shown in the figure below, Mac computers can view the DNS used by the current network in "System Preferences - Network - Wi-Fi - Advanced - DNS". Why do we never need to set up a DNS server? This is because most modern routers have the function of a DHCP server, which automatically provides us with the default DNS server address. The router will set the DNS server address of all devices connected to it as its own IP address. The DNS requests of mobile phones, computers and other network devices connected to the router are uniformly sent to the router IP address. At this time, the router acts as the DNS server of each device. Then, the router forwards the DNS request to the actual DNS server. The actual DNS server resolves the domain name IP and returns it to the router. Finally, the router returns the IP to the terminal device. Sending a DNS request to a DNS server to obtain the real IP address of a website takes a certain amount of time. One of the factors that affect this time is the geographical location of the DNS server. The closer the DNS server is to you, the faster the data transmission will be. Therefore, by default, the router will obtain the nearest DNS server address from the network provider to achieve the fastest network response. 2. ARP Once the IP address is determined, an IP datagram can be sent to the destination address. However, at the underlying data link layer, it is necessary to know the MAC address corresponding to each IP address for actual communication. Therefore, a method is needed to obtain the MAC address of the destination host based on its IP address. This is what the ARP protocol does. The so-called address resolution is the process of the host converting the target IP address into the target MAC address before sending the frame. In addition, when the sending host and the destination host are not in the same LAN, even if they know each other's MAC address, they cannot communicate directly and must be forwarded through routing. Therefore, at this time, the sending host will not obtain the real MAC address of the destination host through the ARP protocol, but the MAC address of a router that can access the outside of the LAN. Therefore, all frames sent from the sending host to the destination host will be sent to the router and sent out through it. This situation is called delegated ARP or ARP proxy. (1) ARP working principle How does ARP know the MAC address? Simply put, ARP determines the MAC address with the help of two types of packets: ARP request and ARP response. There is an ARP cache table in every computer or router with TCP/IP protocol installed. The IP addresses and MAC addresses in the table correspond to each other, as shown in the following table. Take host A (192.168.38.10) sending data to host B (192.168.38.11) as an example.
It should be noted that Host A and Host B in the example belong to the same network segment. If Host A and Host B do not belong to the same network segment, then Host B will not be able to receive the broadcast (ARP request) sent by Host A. Therefore, before sending a broadcast (ARP request), host A will determine whether host B belongs to the same network segment. If not, it will search for the MAC address of the gateway (router) in its own ARP cache table. If not found, host A will send a broadcast (ARP request) on the network to inquire about the MAC address of the gateway (router). The ARP cache table uses an aging mechanism. If a row in the table is not used for a period of time, it will be deleted. This can reduce the length of the cache table and speed up the query. (2) View the local ARP How to view the local ARP cache table?
3. DHCP It would be very tedious to set IP addresses for each host one by one. Therefore, in order to achieve automatic setting of IP addresses and unified management of IP address allocation, the DHCP protocol was created. As shown in the figure below, the Mac computer can view the current local IP configuration in "System Preferences - Network - Wi-Fi - Advanced - TCP/IP". The DHCP server will centrally manage the IP address allocation range, subnet mask, default route, and DNS server for each subnet. With DHCP, computers can communicate over TCP/IP as long as they are connected to the network. In other words, DHCP makes plug-and-play possible. DHCP can be used not only in IPv4 but also in IPv6. (1) DHCP working mechanism Before using DHCP, you must first set up a DHCP server (often the router of the network segment is used as a DHCP server). Then set the IP address to be assigned by DHCP on the server. In addition, you also need to set the corresponding subnet mask, routing control information, and DNS server address on the server. After the DHCP server is set up, the operation of DHCP is divided into four basic processes, namely requesting an IP lease, providing an IP lease, selecting an IP lease, and confirming an IP lease. The so-called lease is the validity period of the computer IP address. This completes the DHCP network settings and enables TCP/IP communication. When an IP address is no longer required, a DHCP cancel packet can be sent. In addition, the DHCP client can send a DHCP request packet before the IP lease expires to notify that it wants to extend the time limit. 4. NAT Let me tell you an interesting experiment. Pick up your mobile phone and computer, connect to the same Wi-Fi, then visit Baidu and enter "IP". You will be surprised to see that the IP addresses displayed on the mobile phone and computer are the same, and they are not the local IP address. Then the question is, in the process of sending data packets, the location is based on the source IP address and destination IP address of the network layer. According to the results of the above experiment, the source IP addresses of the same LAN are obviously the same public network IP, so how is the data packet responded by Baidu accurately sent to our local computer? The answer is to use NAT technology. NAT (Network Address Translator) is used to use private addresses in the local network and use global IP addresses when connecting to the Internet. In addition to converting IP addresses, NART (Network Address Ports Translator) technology has also emerged that can convert TCP and UDP port numbers, thereby enabling communication with multiple hosts using one IP address. Most of what we call NAT now is NAPT, or IP masquerade. NAT (NAPT) is actually a technology developed for IPv4, which is facing address exhaustion. However, IPv6 is also using NAT to improve network security, and NAT-PT is often used in mutual communication between IPv4 and IPv6. (1) NAT working mechanism As shown in the figure below, take the communication between the host at 10.0.0.10 and the host at 163.221.120.9 as an example. Using NAT, the NAT router on the way converts the source address from 10.0.0.10 to the global IP address (202.244.174.37) before sending the data. Conversely, when the packet is sent from the address 163.221.120.9, the destination address (202.244.174.37) is first converted to the private IP address 10.0.0.10 before being forwarded. NAT modifies the IP header of the data packet. Since the IP address is also used for checksum calculation in TCP or UDP, when the IP changes, the TCP or UDP header also needs to be converted accordingly. Inside the NAT (NAPT) router, there is an automatically generated table for address translation. This table is generated when 10.0.0.10 sends the first packet to 163.221.120.9, and is processed according to the mapping relationship in the table. When multiple machines in a private network need to communicate with the outside world at the same time, people will inevitably worry about whether the global IP address is insufficient if only the IP address is converted. At this time, the method of converting the port number together (NAPT) as shown in the following figure can solve this problem. As shown in the figure, the port number of the host 163.221.120.9 is 80, and there are two clients 10.0.0.10 and 10.0.0.11 communicating at the same time in the LAN, and the local ports of these two clients are both 1025. At this time, simply converting the IP address to a global address 202.244.174.37 will make all the numbers after conversion completely consistent. Therefore, the problem can be solved by converting the port number of 10.0.0.11 to 1026. By merging the oval contents in the above figure to generate a conversion table for a NAPT router, the combination of address and port can be correctly converted, allowing clients A and B to communicate with the server at the same time. This translation table is automatically generated on the NAT router. For example, in the case of TCP, this table is generated once the SYN packet is sent when the TCP connection is first handshaked. It is then deleted from the table as the confirmation response of the FIN packet sent when the connection is closed is received. In the communication using TCP or UDP, only when the destination address, source address, destination port, source port and protocol type (TCP or UDP) are all the same, it is considered as the same communication connection, that is, the same row record in the multiplexing conversion table. 5. ICMP When building an IP network, you need to pay special attention to two points: confirming that the network is working properly and diagnosing problems when anomalies are encountered. For example, if a network has just been built, you need to verify whether the network settings are correct. ICMP is a protocol that provides this kind of function. The main functions of ICMP include confirming whether the IP packet is successfully delivered to the destination address, notifying the specific reasons why the IP packet is discarded during the sending process, improving network settings, etc. With these functions, you can obtain information such as whether the network is normal, whether the settings are incorrect, and whether there are any abnormalities in the equipment, which makes it easier to diagnose problems on the network. In IP communication, if an IP packet fails to reach the destination address for some reason, then ICMP will be responsible for notifying the specific reason. For example, host A sends a data packet to host B. For some reason, the router on the way fails to find the existence of host B. At this time, the router will send an ICMP packet to host A, indicating that the packet sent to host B failed. ICMP messages can be roughly divided into two categories: one is error messages that notify the cause of the error, and the other is query messages used for diagnosis. 6. ping Ping is a computer network tool that uses the ICMP protocol to test whether a data packet can reach a specific host through the IP protocol. The operating principle of ping is to send an ICMP request echo packet to the target host and wait for the echo reply packet to be received. The program will estimate the packet loss rate (packet loss rate) and the round-trip delay time (network delay) of the packet according to the time and the number of successful responses. Ping is sometimes used as a verb, such as "ping computer XXX to see if it is turned on." The following example uses pinging Baidu's URL: As you can see, Baidu's IP address is 61.135.169.125. When tested with 64 bytes, the response time is 5.589 milliseconds and the TTL (Time To Live) value is 56. Here we have to explain what TTL is? There is a field in the IP packet called TTL (Time To Live), and its value decreases by 1 each time it passes through a router until it reaches 0 and the IP packet is discarded. At this point, the IP router will send an ICMP timeout message to the sending host and notify that the packet has been discarded. In the example, the TTL value is 56. Assuming that the TTL set by the sender is 64, the number of routes in the middle is 64 - 56 = 8. end According to the OSI seven-layer model, HTTP datagram is the application layer, with a TCP header attached to the transport layer to indicate the source port number and the destination port number, an IP header attached to the network layer to indicate the IP addresses of the sender and receiver, and the upper layer protocol number (TCP/UDP), and an Ethernet header attached to the data link layer to indicate the MAC address of the receiver and the MAC address of the sender. This is your previous understanding. After studying this article, I believe you can understand the configuration of the local IP address, subnet mask, the local MAC address, the destination machine IP address, and the acquisition of other machine MAC addresses. |
<<: 10 SD-WAN projects to watch
Recommend
China Mobile: More than 560,000 5G base stations have been built
At the 2021 China Mobile Global Partner Conferenc...
5G standardization work encounters obstacles, and the launch of standards may be delayed
The high-speed 3GPP 5G standard work may encounte...
Exploring cross-industry collaboration between 5G and edge computing
The combination of 5G networks and edge computing...
Energy-saving building 5G solutions are the key to green buildings
Building equipment suppliers are prioritizing gre...
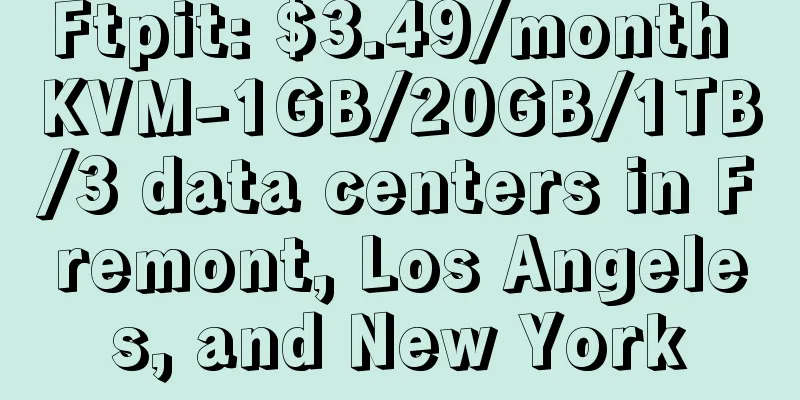
TNAHosting: 12G memory 500GB hard disk OpenVZ monthly payment from $5, 4G memory KVM monthly payment of $5
Some businesses give people the impression that t...
my country has built the world's largest 4G network
On January 6, the Ministry of Science and Technol...
5G spending of the three major operators decreased, and the number of package users increased
The three major operators recently released their...
Adhering to independent innovation, China Cloud Technology has deepened its roots in application delivery
[51CTO.com original article] 2021 is the first ye...
How much money has 5G burned? The accounts of the three major operators are all here
In 2020, the country's top leadership has cla...
Key 5G limitations facing enterprises
As interest in 5G cellular technology grows, ente...
Outlook for domestic 5G development in 2021 (Part 3): Opportunities
From the official launch of commercial use in 201...
80VPS: Japan/Hong Kong CN2 server 600 yuan/month, E5/16G/1TB/20M bandwidth
80VPS is an early-established comprehensive netwo...
The dangers and opportunities of 5G construction in my country under the influence of the epidemic
2020 is the starting point for the outbreak of th...
2017Q1 China Wireless Router Market Research Report
With the popularity of WiFi and mobile devices, w...
For the first time in 21 years! SpaceX acquires satellite communications startup
On August 9, according to foreign media reports, ...

![[Restock] Bricklayer Los Angeles CN2 GIA (DC6/DC9)/Japan Softbank special price $46.6/year](/upload/images/67cabd08b768b.webp)